A team of security researchers found that several modern Honda car models have a vulnerable rolling code mechanism that allows unlocking the cars or even starting the engine remotely.
Called Rolling-PWN, the weakness enables replay attacks where a threat actor intercepts the codes from the keyfob to the car and uses them to unlock or start the vehicle.
The researchers claim to have tested the attack on Honda models between 2021 and 2022, including the popular models below:
- Honda Civic 2012
- Honda X-RV 2018
- Honda C-RV 2020
- Honda Accord 2020
- Honda Odyssey 2020
- Honda Inspire 2021
- Honda Fit 2022
- Honda Civic 2022
- Honda VE-1 2022
- Honda Breeze 2022
Intrinsic weakness
The keyless entry system in modern cars rely on rolling codes produced by a pseudorandom number generator (PRNG) algorithm to ensure that unique strings are used each time the keyfob button is pressed.
The rolling code mechanism was introduced to prevent fixed code flaws that enabled man-in-the-middle replay attacks like the one we covered in March, which is still exploitable in older models.
Vehicles have a counter that checks the chronology of the generated codes, increasing the count upon receiving a new code. Non-chronological codes are accepted, though, to cover situations of accidental presses of the keyfob, or when the vehicle is out of range.
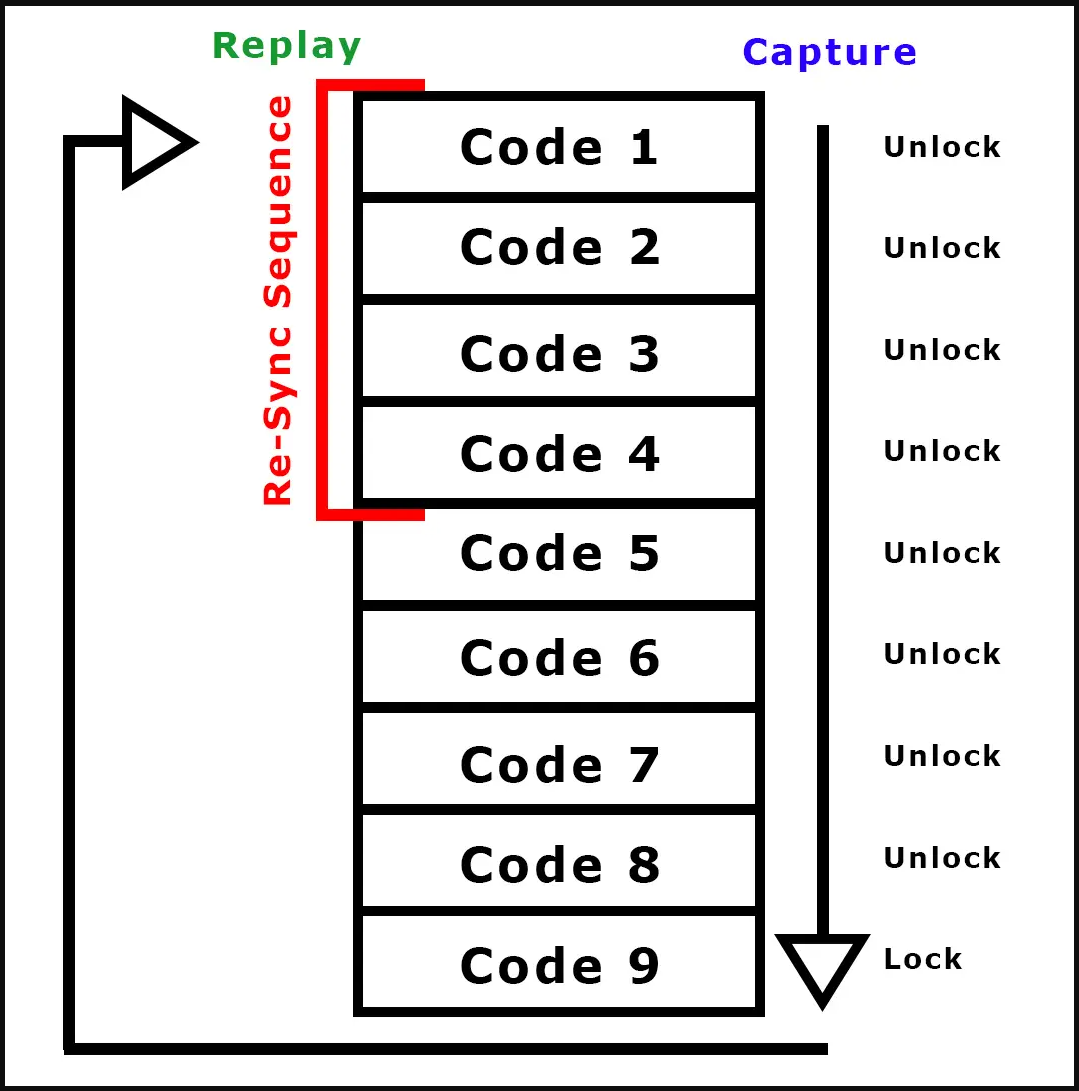
Researchers Kevin2600 and Wesley Li found that the counter in Honda vehicles is resynchronized when the car vehicle gets lock/unlock commands in a consecutive sequence. This causes the car to accept codes from a previous session, which should have been invalidated.
An attacker equipped with software-defined radio (SDR) equipment could capture a consecutive sequence of codes and replay them at a later time to unlock the vehicle and starts its engine.
The researchers provided details about the Rolling-PWN issue along with several videos showing how it could be used to unlock various Honda models.
The vulnerability is tracked as CVE-2021-46145 (medium severity) and is described as an issue “related to a non-expiring rolling code and counter resynchronization” in the keyfob subsystem in Honda.
At the time it was disclosed, in December 2021 [1, 2], the tests were carried on an Honda Civic from 2012. However, newer models are also vulnerable.
Automotive journalist Rob Stumpf was able to replicate Rolling-PWN on his 2021 Honda Accord by capturing codes at different times.

He explains that as long as the re-sync sequence is replayed, it doesn’t matter if days or months have passed since capturing the codes; the attacker would still be able to re-sync and perform the unlock action.
Stumpf notes that even if an attacker could use Rolling-PWN to start a Honda, they would not be able to drive it away because the keyfob needs to be in proximity.
Honda denies there’s a problem
The researchers tried to notify Honda of the vulnerability but could not find a contact for reporting security-related issues. In the end, they filed a report to Honda Customer Service but have not heard back.
In a statement to Vice, a spokesperson for Honda stated that the report wasn’t credible and that the allegations are unfounded.
“The key fobs in the referenced vehicles are equipped with rolling code technology that would not allow the vulnerability as represented in the report,” stated Honda.
“In addition, the videos offered as evidence of the absence of rolling code do not include sufficient evidence to support the claims,” the company added.
If Honda finds the Rolling-PWN research valid, addressing the problem would prove difficult since it is necessary to upgrade the vulnerable firmware.
Newer models may support OTA (over the air) updates, but Rolling-PWN will be a lot harder to remediate on older models that do not.
BleepingComputer has also reached out to Honda for clarifications on the above, and we will update this story once we receive a response.




















